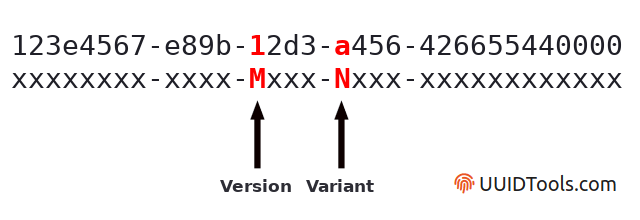
An example of a 36-character string depicting a 128-bit binary value in... | Download Scientific Diagram

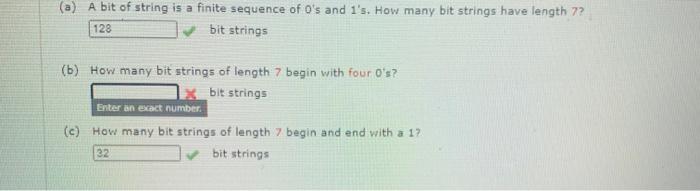
8, 16, 32, 64 & 128-Bit Integer Limit | Processor & Data Types - Video & Lesson Transcript | Study.com

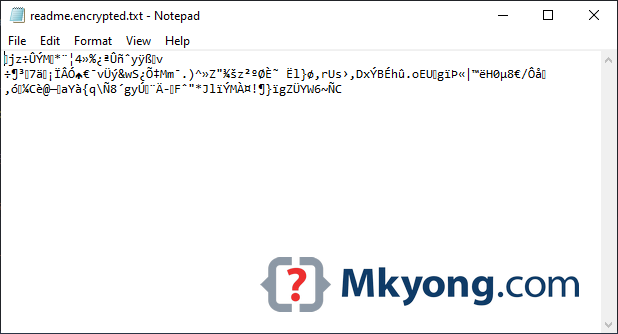
Igor's Tip of the Week #128: Strings list - Malware Analysis - Malware Analysis, News and Indicators