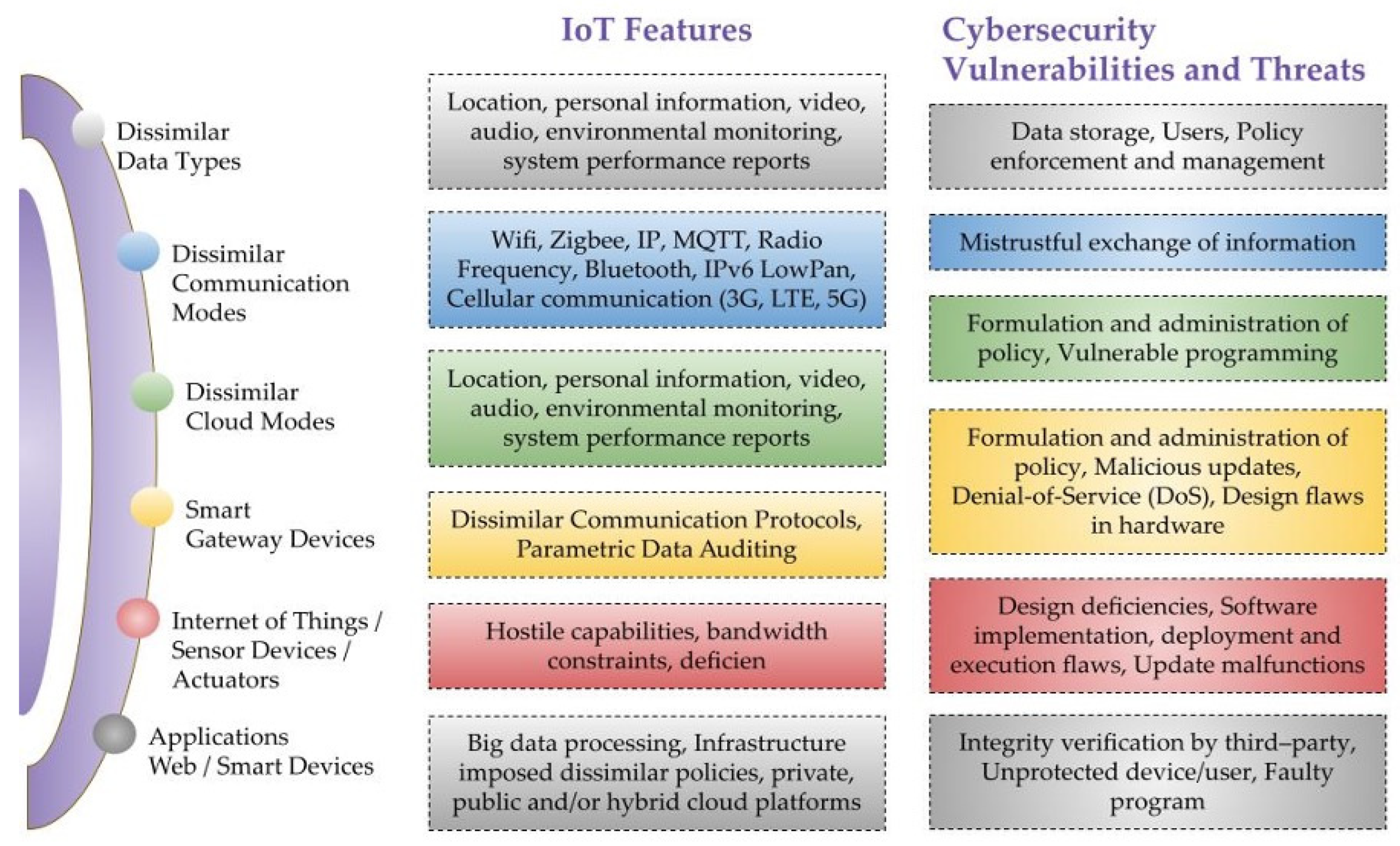
Sensors | Free Full-Text | A Critical Cybersecurity Analysis and Future Research Directions for the Internet of Things: A Comprehensive Review
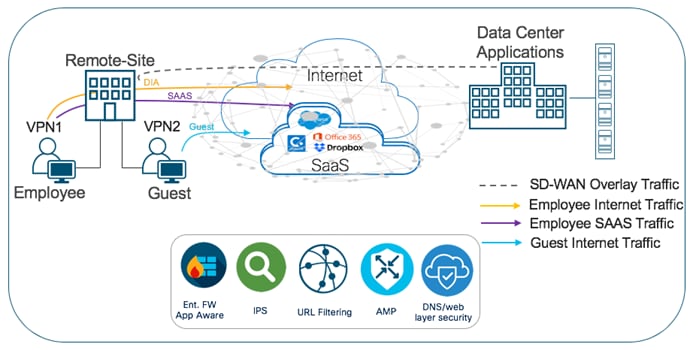
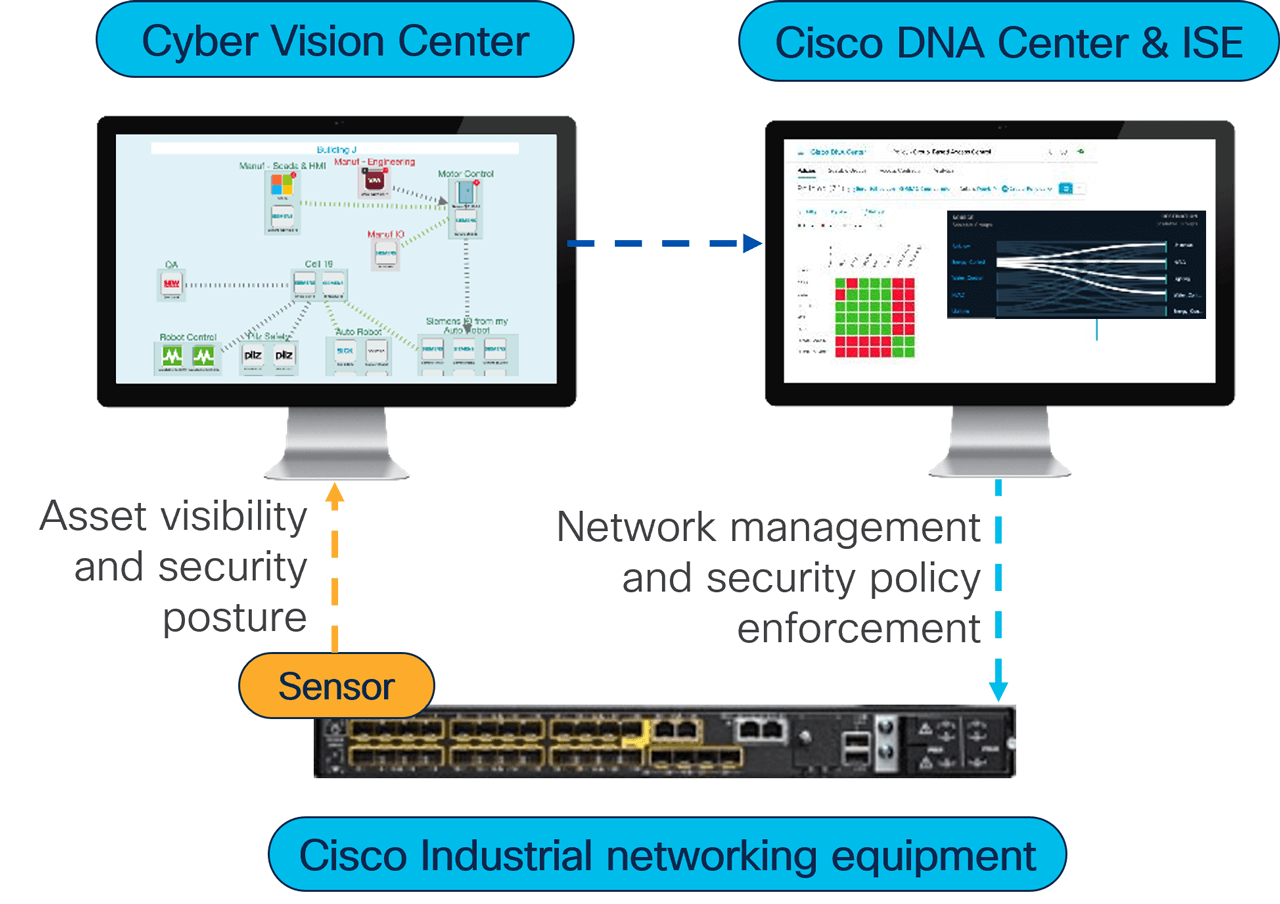
Deploying Identity and Mobility Services within a Converged Plantwide Ethernet Architecture Design and Implementation Guide

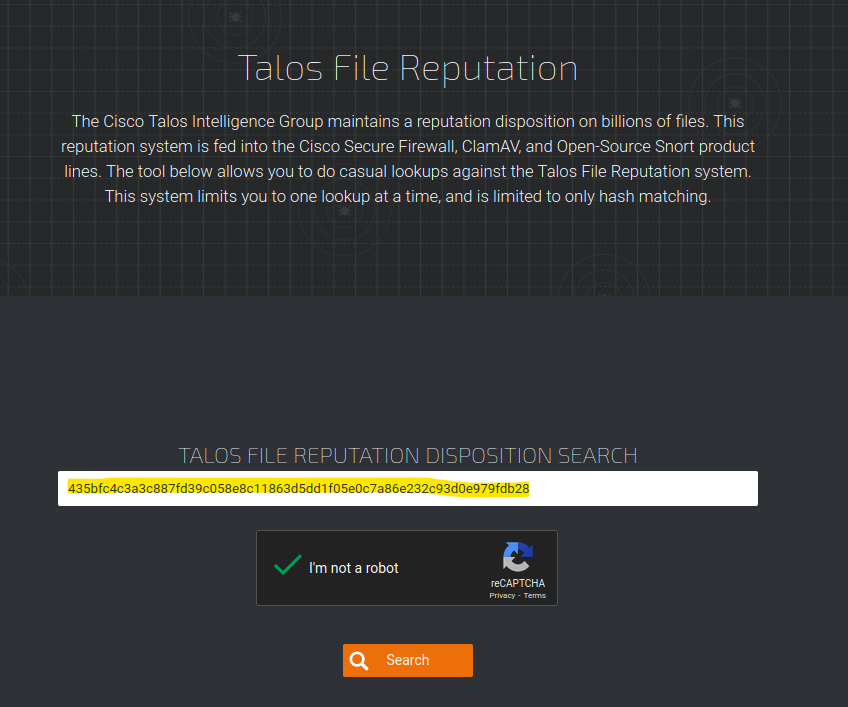
Vulners – Google for hacker. How the best vulnerability search engine works and how to use it | Alexander V. Leonov